Tinker, tailor, soldier, spy. And then there's Edward Snowden, who was a spy and then became something else. Nobody is neutral about him. The other day I heard a senior military officer describe him unambiguously as "a thief." In Washington he seems to be universally regarded as a traitor. Many people in Europe regard him as, at worst, a principled whistleblower and, at best, a hero in the Daniel ("Pentagon Papers") Ellsberg mold.
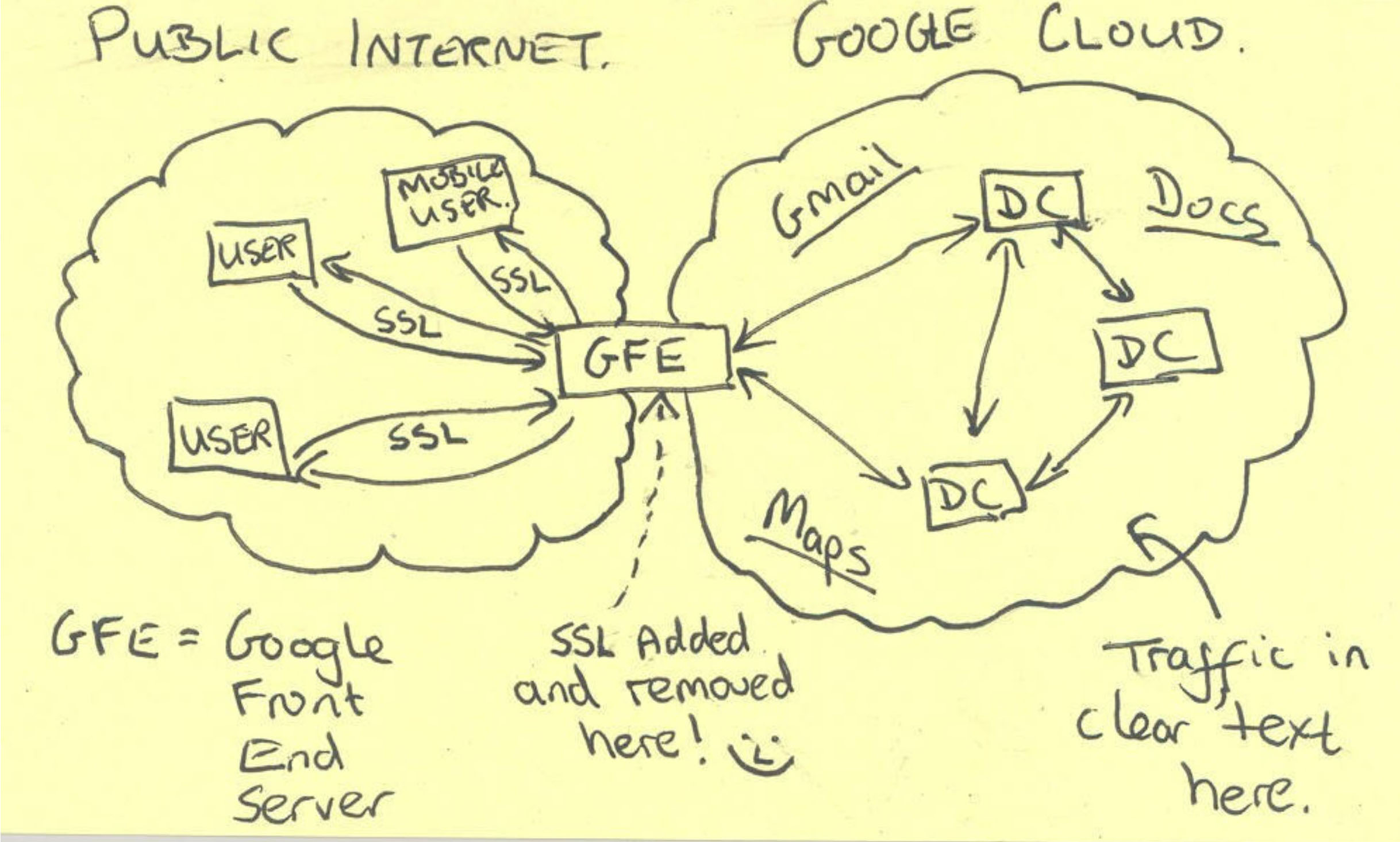
Whatever you think about him, though, one thing is clear: Snowden is a pretty astute geek. The evidence for this is in the way he approached his whistleblowing task. Having concluded (as several other National Security Agency employees before him had) that the NSA had misinterpreted or overstepped its brief, he then identified prominent instances of agency overreach and for each category downloaded evidence that supported his conjecture.
We're now getting to the point where we can begin to assess the bigger picture. What do the Snowden revelations tell us about what's wrong with the NSA — and its leading overseas franchise, Britain's GCHQ?

















With your current subscription plan you can comment on stories. However, before writing your first comment, please create a display name in the Profile section of your subscriber account page.