A series of major cyberattacks in recent weeks has underscored the brazenness of the attackers and the challenges of tackling the problem of ransomware, just as the Biden administration announced plans to take on the issue.
In a matter of days, attacks were revealed against the police department in Washington, where the hackers threatened to release information about police informants to criminal gangs; the Illinois Attorney General’s office, which had been warned about weak cybersecurity practices in a recent state audit; and San Diego-based Scripps Health, where medical procedures were canceled and emergency patients diverted to other hospitals.
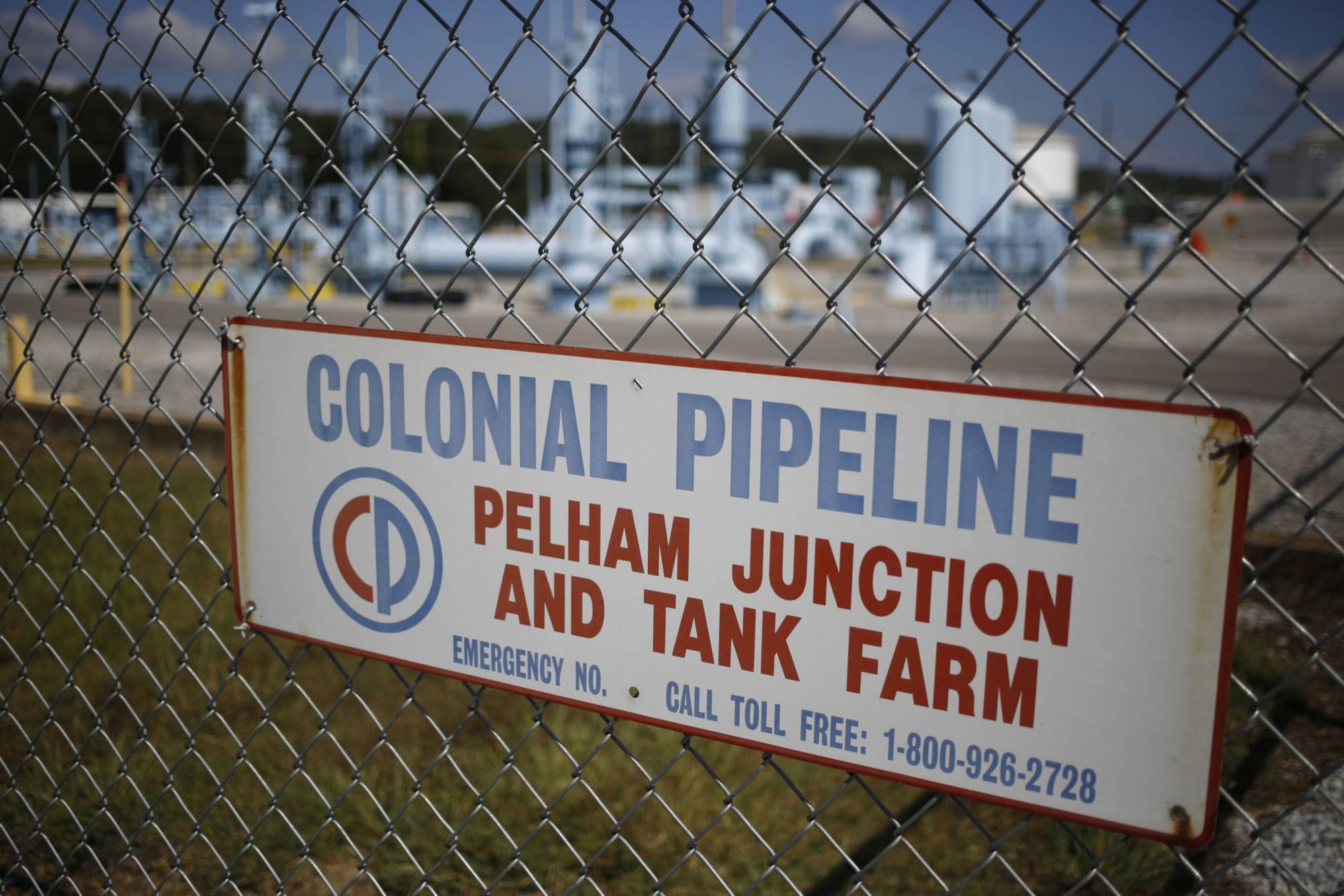
Then on Saturday, Colonial Pipeline confirmed that it had joined the list of recent ransomware victims in an attack that threatened to upend gasoline and diesel supplies on the East Coast. While few details about the attack are yet known, Colonial shut down the biggest gasoline pipeline in the U.S. as part of an effort to contain the threat.